Posts tagged on Analysis
Analysis of a Redline Based Malware
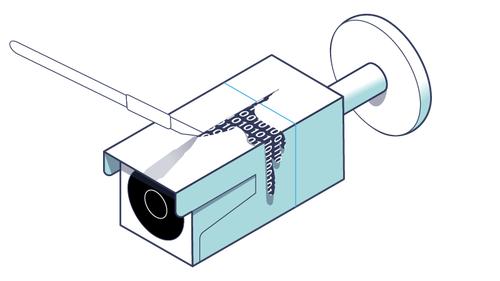
– In recent months, there have been increasing attempts to spread malware via some seemingly ‘harmless’ programs, luring the user through rewards such as sending money with cryptocurrency or NFT-themed gifts. The unsuspecting user by running an ‘innocent’ executable to access prizes becomes part of a botnet. See Full Article
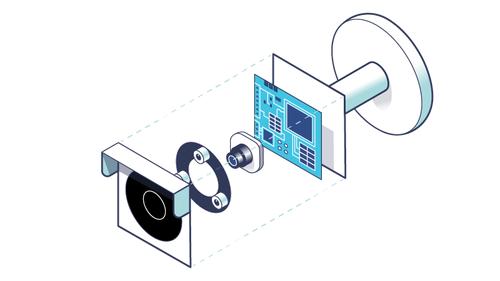
Reverse Engineering the OMNIVISION OS12D40 Driver
– In Part 6 of our series, we structured a theoretical discussion regarding the devices, how they communicate, and the hardware elements that enable this. See Full Article
Techniques for Setting up Peripherals via PIO and DMA
– In Part 5 of our series, we focused our efforts on understanding how the firmware was structured. In doing so, we analyzed the folder with the system executables and delved into the various configuration files. See Full Article
Exploring the Operating System of Reolink RLC-810A
– In Part 4 of our series, we focused on the file system and before concluding, we were able to extract files from two UBIFS images contained within the firmware. Here in Part 5, we will try to better understand the structure of the root file system by introducing some basic concepts of the operating system used by Reolink RLC-810A, namely Linux. See Full Article
Understanding the UBI File System in Embedded Devices
– In Part 3 of our series, we explored the hardware device elements of the Reolink RLC-810A ― focusing on the NAND memory. We continue with Part 4 of our exploration into an IP camera firmware through introducing the concept of a file system. Furthermore, we will explore the technical reasons for choosing the UBI File System (UBIFS), a file system used especially for a category of mass storage, and … See Full Article
Dissecting Reolink RLC-810A Hardware: A Detailed View
– Now that we know how device booting works, let’s try to extract some parts from the firmware that we downloaded in Part 1 of our series. Here, we are interested in two main sections: the Linux kernel (which takes care of booting the device services) and the flattened device tree (which allows the kernel to know the hardware configuration a priori without inspecting each device). See Full Article
Booting an Embedded OS: the Booting and U-Boot Phase
– In the first post, we introduced embedded devices and started to scour through and extract information from Reolink IP camera firmware. At the end of the post, we ran Binwalk, which showed various types of files such as Flattened Device Tree, uImage Header, and UBI File System. See Full Article
Introduction to Firmware Analysis of a Reolink IP Camera
– Embedded devices continue to increase in popularity and one category, in particular, that has become en vogue as of late is the Internet of Things (IoT). The emergence of these next generation technologies has driven the home automation evolution from simple light bulbs to cloud-connected printers, smart refrigerators, etc. See Full Article
Unveiling the Anonymous Author: Stylometry Techniques
– One of the techniques that fascinates me most about writing is textual analysis, which includes semantics (the meaning of words) and syntax (the use of signs and letters to construct sentences). See Full Article
Analyzing the Mario Themed Malware
– If you were a child with a Nintendo DS like myself, growing up you will undoubtedly have played (for countless hours) video games from the Mario series. Appearing for the first time in Donkey Kong, Mario is the undisputed protagonist of the video game brand of the Nintendo development house ― from sports to cars, most of the famous video games produced by Nintendo have Mario as the main character. See Full Article
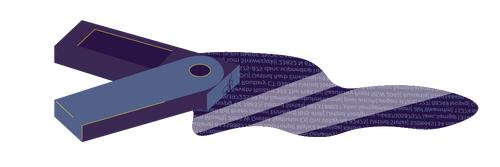
How to React to the Ledger Data Breach: 5 Recommendations
– If you think you are amongst the users affected by the latest Ledger data breach, it is important not to panic! Follow a few simple steps and you can check the extent of the damage and keep an eye on the security of your account. See Full Article
The Myth of Privacy and End-to-End Encryption in Zoom
– Zoom is a service to host meetings without the need to install and configure complicated applications: it is one of the many solutions for those who, during quarantine, want to keep in touch with friends and relatives. See Full Article
Take off the Infrastructure of a Scammer: Cryptonder and Torowallet
– On a rainy autumn day, I was contacted like many users by a suspicious individual on Telegram. He insisted on asking for the help of the user who had to recover his wallet which contained several bitcoins. Our ‘friend’, hencereferred as ‘Z.’, insisted that the user has to register on the platform to be able to unlock his wallet at the price of 0.3 BTC. See Full Article
Monero Windows and Linux CLI Compromised: The Analysis of Binaries
– As mentioned in the getmonero.org blog post, the binaries of Command Line Interface (CLI) of Monero were recently compromised. See Full Article
Unpacking ASIC firmware: AntMiner Exploited
– Experts say cryptocurrencies (such as Bitcoin, Monero, and Ethereum) will be the protagonists of the future decentralized and distributed economic system. If this is true then one of the most debated topics in the field of cryptocurrency, how to verify payments while spending as little as possible in terms of resources, is especially important for cryptosecurity. See Full Article
Botnet analysis based on IRC network
– With one of my many honeypots actived around the world wide web, I discovered an interesting script written with the famous Perl programming language. This Perl script is a malware used to remotely control a machine, opening what is technically called backdoor. If this malicious program runs on multiple machines, there is a possibility that the attacker may have created a botnet. See Full Article
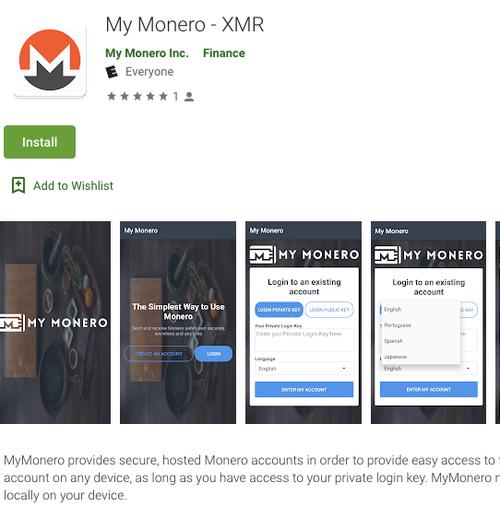
MyMonero Phishing – Reversing the fake Android app
– With one of my many honeypots actived around the world wide web, I discovered an interesting script written with the famous Perl programming language. This Perl script is a malware used to remotely control a machine, opening what is technically called backdoor. If this malicious program runs on multiple machines, there is a possibility that the attacker may have created a botnet. See Full Article
MEGA Chrome Extension Hacked - Detailed Timeline of Events
– On 4 September at 14:30 UTC, an unknown attacker managed to hack into MEGA’s Google Chrome web store account and upload a malicious version 3.39.4 of an extension to the web store, according to a blog post published by the company. Upon installation or auto-update, the malicious extension asked for elevated permissions to access personal information, allowing it to steal login/register … See Full Article
Introduction to MoneroV and its Inherent Risks
– The “MoneroV” coin is an impending unofficial fork of the Monero blockchain with many “red flag” characteristics that have alarmed the Monero community. Many users are wondering: could the MoneroV fork be a scam project? This article discusses risks for individuals claiming MoneroV, and describes how MoneroV opens an attack vector on the overall privacy of the Monero network itself. See Full Article
How to Crash the iPhone with a Single Telugu Character
– In recent years, Apple has been heavily criticized for the security implications of their market centralization and policy of irreversible operating system updates. Mobile device users are strongly pressured to install packaged iOS upgrades that cannot be rolled back. While this practice greatly increases security for most users, there is an inherent danger to this centralization. See Full Article
How I broke Envato Search Engine
– Envato devs had not developed a strong filter in order to avoid any XSS Attack, and I noticed that I could perform a XSS Injection. I have contacted Envato and, after some investigations, they have discovered that my vulnerabilities were critical! They thanked me and patched the vulnerabilities within 5 business days. Good job Envato!! See Full Article
Technical Analysis of WannaCry Ransomware
– By now, on the net, on TV and around the world, there is nothing but talk about WannaCrypt: ransomware, or malware that can encrypt all the files on one’s computer and demand a ransom for unlocking them. See Full Article