Latest articles
Analysis of a Redline Based Malware
– In recent months, there have been increasing attempts to spread malware via some seemingly ‘harmless’ programs, luring the user through rewards such as sending money with cryptocurrency or … Read Full Article
Reverse Engineering the OMNIVISION OS12D40 Driver
– In Part 6 of our series, we structured a theoretical discussion regarding the devices, how they communicate, and the hardware elements that enable this. Read Full Article
Techniques for Setting up Peripherals via PIO and DMA
– In Part 5 of our series, we focused our efforts on understanding how the firmware was structured. In doing so, we analyzed the folder with the system executables and delved into the various … Read Full Article
Exploring the Operating System of Reolink RLC-810A
– In Part 4 of our series, we focused on the file system and before concluding, we were able to extract files from two UBIFS images contained within the firmware. Here in Part 5, we will try to better … Read Full Article
Biography
I am a security engineer, a writer, and contributor to the Monero project, a cryptocurrency focused on preserving privacy for transactions data. My publication Mastering Monero has became one of the best rated resources to learn about Monero.
Contact
Have you got any questions? Would you like to know more about my books? Would you want to suggest me an article? Or report any particular malware?
Feel free to reach me via email hi@serhack.me or Twitter. For any email corrispondence, please encrypt your email with my PGP public key.
Would you like to know what I'm working on?
Publications
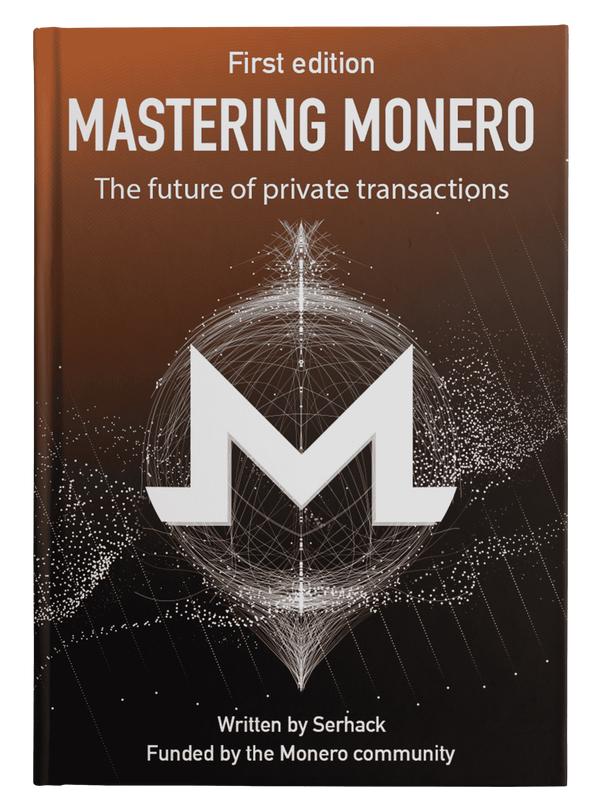
Mastering Monero
It is your guide through the world of Monero, a leading cryptocurrency with a focus on private and censorship-resistant transactions. This book contains everything you need to know to start using Monero in your business or day-to-day life, even if you’ve never understood or interacted with cryptocurrencies before.
Breaking Cryptocurrencies
The resource for learning more information about possible attack vectors applied to the blockchain field. Through a simple approach, the reader will understand how a cryptocurrency works and what are the minimal requirements for defying a blockchain. After understanding the techniques needed to analyze and monitor their own cryptocurrency project, the readers will know what the most common attacks are and ways to prevent them.
What They Say About Me
"SerHack does an excellent job of presenting blockchains and cryptocurrency concepts in a clear and concise way."
–Austin Gilbert via Goodreads.com on Mastering Monero"SerHack is not only a very smart security researcher and talented programmer, he has a keen eye for the implications of technology on our everyday lives."
–Andrés Fernández Cordón via Linkedin"Productivity Monster is the phrase that comes to mind when I think about SerHack. I was impressed with his ability to always be available to help me out during the design process and be positive when facing road bumps."
–Gustaf (Baltsar) Garnow via Linkedin