All Articles
Started to be written in 2017, SerHack Blog represents a solid but unique point of view in Computer Science field. From cryptocurrencies to information security, from reverse engineering to phishing: many topics are depicted using layman terms. What are you waiting for? Read one of any articles.

Analysis of a Redline Based Malware
– In recent months, there have been increasing attempts to spread malware via some seemingly ‘harmless’ programs, luring the user through rewards such as sending money with cryptocurrency or NFT-themed gifts. The unsuspecting user by running an ‘innocent’ executable to access … See Full Article
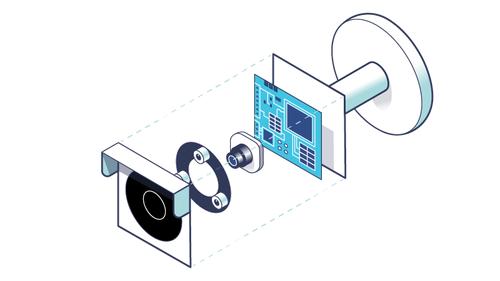
Reverse Engineering the OMNIVISION OS12D40 Driver
– In Part 6 of our series, we structured a theoretical discussion regarding the devices, how they communicate, and the hardware elements that enable this. See Full Article
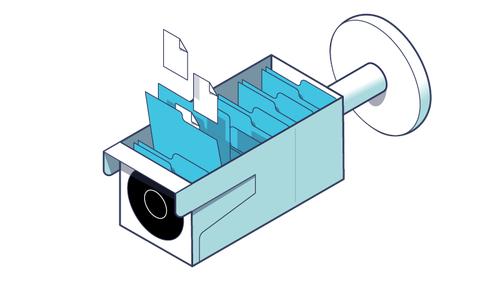
Techniques for Setting up Peripherals via PIO and DMA
– In Part 5 of our series, we focused our efforts on understanding how the firmware was structured. In doing so, we analyzed the folder with the system executables and delved into the various configuration files. See Full Article
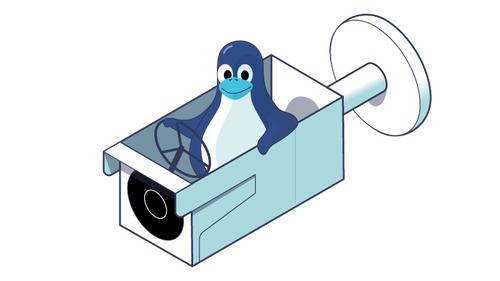
Exploring the Operating System of Reolink RLC-810A
– In Part 4 of our series, we focused on the file system and before concluding, we were able to extract files from two UBIFS images contained within the firmware. Here in Part 5, we will try to better understand the structure of the root file system by introducing some basic concepts of the operating … See Full Article
Understanding the UBI File System in Embedded Devices
– In Part 3 of our series, we explored the hardware device elements of the Reolink RLC-810A ― focusing on the NAND memory. We continue with Part 4 of our exploration into an IP camera firmware through introducing the concept of a file system. Furthermore, we will explore the technical reasons for … See Full Article
Dissecting Reolink RLC-810A Hardware: A Detailed View
– Now that we know how device booting works, let’s try to extract some parts from the firmware that we downloaded in Part 1 of our series. Here, we are interested in two main sections: the Linux kernel (which takes care of booting the device services) and the flattened device tree (which allows … See Full Article
Booting an Embedded OS: the Booting and U-Boot Phase
– In the first post, we introduced embedded devices and started to scour through and extract information from Reolink IP camera firmware. At the end of the post, we ran Binwalk, which showed various types of files such as Flattened Device Tree, uImage Header, and UBI File System. See Full Article
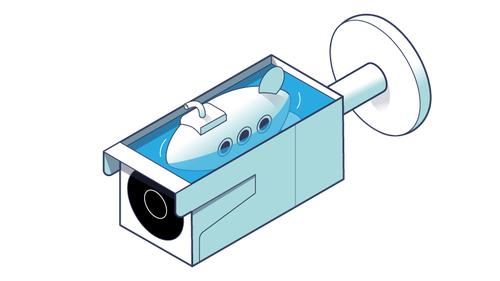
Introduction to Firmware Analysis of a Reolink IP Camera
– Embedded devices continue to increase in popularity and one category, in particular, that has become en vogue as of late is the Internet of Things (IoT). The emergence of these next generation technologies has driven the home automation evolution from simple light bulbs to cloud-connected printers, … See Full Article
The Story Behind the Alternative Genesis Block of Bitcoin
– In this article, I attempt to explain the early source code of Bitcoin and make correlations with the source code currently in use. My intent is to help you better understand the early details regarding the history of Bitcoin and the enigmatic figure of Satoshi Nakamoto. As far as newcomers to … See Full Article
Unveiling the Anonymous Author: Stylometry Techniques
– One of the techniques that fascinates me most about writing is textual analysis, which includes semantics (the meaning of words) and syntax (the use of signs and letters to construct sentences). See Full Article